Going online has become a need for our daily lives in the era we live in today. However, as much as it is essential to have an online presence, it is also important to understand its various aspects to protect ourselves from potential cyber threats . Having an online presence may open doors to making confidential and personal information easily accessible to threats actors.
As a result, you have to be more conscious in terms of the security of your personal data. Not only do cyber-attacks put you at a financial loss, but they also damage your reputation and business.
One of the most typical types of cyber attacks that involve stealing data is phishing . According to the IRONSCALES State of Cybersecurity Report , more than 81% of organizations have experienced an increased rate of phishing attacks since March 2020.
In phishing, cyber criminals use different types of tactics, such as sending emails, text messages, or making phone calls, to trick victims into revealing their private information. One of the types of phishing is trap phishing. It is the technique of trapping victims into clicking a link containing malware or downloading malware.
Let us discuss what exactly trap phishing is in detail in this blog post. Also, we shall discuss the types of trap phishing, how it differs from typical phishing, and how to recognize and prevent it.
What is Trap Phishing?
It is one of the most favored methods for cybercriminals to attack victims. The phrase "trap phishing" refers to phishing attempts trying to lure the victims into downloading malware or clicking on a link to malware. These emails pretend to be from well-known and reputed companies. They have a tone of urgency to get recipients to divulge personal information, provide money, or visit a phishing website to "change their account data" so the hacker may steal their login information.
In these attacks, the hackers send out cold emails and SMS regularly, observe the pattern, and look for errors. The criminals gain access to all their sensitive information as soon as the victim falls into the trap. This ends up in handing over personal information, making the specified payment, or logging in to a phishing site with the aim of stealing credentials.
How Does Trap Phishing Occur?
Cybercriminals and hackers are always searching for security vulnerabilities in the system of victims. Simple and common human errors can provide a massive opportunity for trap phishing.
Attackers send generic emails, calls, and messages to a large crowd. Additionally, some trap phishing attempts target certain businesses. You can fall for a generic email that must have been sent to hundreds of other people, or you might be the target of someone who has been keeping tabs on you and sends you mail that appears to have originated from a reliable source.
These emails either ask you directly for personal information, such as your bank account number, or contain a link that, when you click it, takes you to the hacker's website.
Other methods may include impersonating someone. Attackers may pretend to be a friend or someone close. Also, they can use honey traps to lure the victim into providing sensitive data. In many cases, criminals use one or many of these methods to curate an attack on an individual carefully.
Once the individual fall into their trap, the attackers might use your personal information to steal money and information or to sell it to third parties. They may also use malware to infect your device and seize control of your system.
How is Trap Phishing Different from Phishing?
Now that you have understood what trap phishing is. You might now be thinking, how is it different from phishing? This section tries to understand the essential differences between trap phishing and phishing.
As the name suggests, the critical objective of trap phishing is to trap or trick the victim. Here, cybercriminals use a large number of methods at their disposal to trick their target. They observe patterns by sending out emails, calls, and SMS. Later, they shortlist their potential targets and start sending targeted attacks and emails. As soon as victims fall prey to such malicious calls and emails, they breach their systems, steal private information, or install harmful malware on their systems.
Phishing is a broader extent of it. In phishing, cybercriminals send malicious emails to hundreds of users, and then they sit and wait to see which one replies or falls into their trap. The target of a phishing attack is not a specific individual but a large crowd. Essentially the success rate of phishing attacks is meager compared to trap phishing, as it is highly specific.
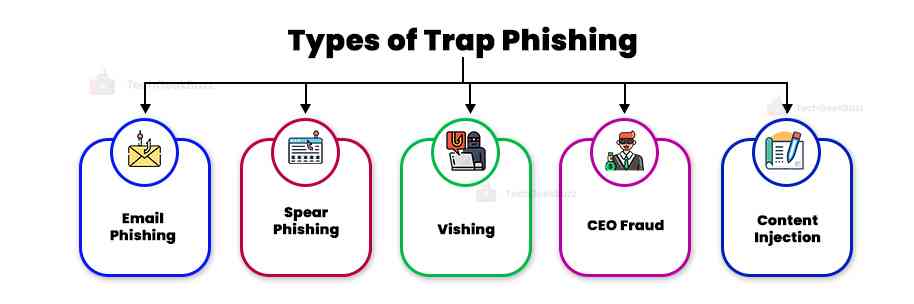
Types of Trap Phishing
This type of phishing takes numerous forms. So, it becomes essential for you to understand each of its forms to avoid falling prey to it. The most common forms are discussed below:
-
Email Phishing
The attackers will send a victim an urgent email; this can contain requests like asking them to update their personal information, confirm their account information, or reset their password. This is the most used phishing method.
-
Spear Phishing
In a spear phishing attack, the criminals do extensive online research on a person or organization before creating a customized email to force them into disclosing personal data.
-
Vishing
Voice phishing or vishing assaults occur when a fraudster calls a victim and leaves a severe message advising the recipient to call another number. Common vishing tactics include convincing the victim that they need to update these facts to compel the victim into exposing their bank account or tax information.
India is one of the most prominent victims of vishing. Due to a lack of knowledge, they often fall into this trap and provide bank information to frauds.
-
CEO Fraud
This threat comprises a fraudster pretending to be a senior executive, like the CEO or CFO, and emailing staff members to ask them to transfer money or divulge essential information. As the communication is from a senior official, the victim often complies with the request without double-checking.
-
Content injection
In a content injection attack, a cybercriminal inserts a malicious link, form, or pop-up into a familiar-looking webpage, such as an email account login page or online banking page. The victim can unknowingly click on any such link, leading to malware attacks.
How to Recognize a Trap Phishing Email?
It is pretty challenging to spot this type of phishing attack as threat imposters impersonate reputed organizations or companies. Here are a few techniques that will help you recognize that certain events are meant to trap you.
-
Check Email Address
One should check the email address to make sure it corresponds to the sender's name and to see if there are any suspicious elements. The URL of the phishing email is often different; this is the biggest giveaway of a phishing email.
Although, it can be challenging to recognize such emails since attackers are very careful in creating them. They take various measures to avoid any kind of suspicion. Often these emails are from trusted significant eCommerce sources or banking services. Due to this, people often overlook the small mistakes in their emails.
-
Check Email Salutation
Another way to recognize trap emails is to look at the salutation of the email. If it is "dear client," "dear customer," or "dear valued customer," this indicates it's a generic communication. If it starts with explicitly addressing you, it might be an email to trick you. This means a cybercriminal is trying to trick you with a "spray and pray" phishing campaign.
-
Tone of Emails
Last, understand whether the email puts you under some time constraints or forces you to perform certain actions quickly. These emails try to get you to act up as fast as possible. They take advantage of the thought process of the victim. As soon as a victim sees an email from a trusted source containing a message like "Update your password immediately", they perform the action without second thoughts, and cyber criminals use this to their advantage. So, if emails make you feel pressured to do certain actions, don’t fall prey to them.
How to Prevent Trap Phishing?
While phishing threats can be challenging to encounter, there are a few easy actions businesses can take to significantly raise their security awareness and lower the chance of data breaches.

-
Make Employees Aware of Phishing Attacks
Employees of an organization are the prime target of cybercriminals. So, it is crucial to provide awareness of phishing attacks to staff members. This can be achieved by giving them access to technologies that simulate real-world phishing scenarios to help them identify and prevent potential threats.
-
Hire Security Executives
Assign security executives to use phishing simulations to track staff awareness of phishing. Additionally, they can deploy phishing modules to instruct, train, and modify employee behavior. To keep phishing and social engineering concerns top of mind, implement phishing simulation and security awareness training platforms.
-
Conduct Campaigns
At regular intervals, organize campaigns regarding phishing and cybersecurity . This involves instructing staff how to choose secure passwords and warning them again about the dangers of emails, attachments, and URLs.
-
Implement Network Access Roles
Try to create network access roles to limit the use of personal devices and set guidelines about sharing business information outside the business environment.
-
Keep Devices and Infrastructure Up-to-date
Ensure all software, operating systems, network tools, and apps are updated, as updated versions are often released to improve security. To help with threat identification, install anti-spam and malware protection software.
Conclusion
Here we have reached the end of our discussion of trap phishing. It is a kind of phishing that involves trapping or tracking victims into disclosing their private information by sending a malicious text or email, or phone call. To avoid becoming a victim of trap phishing, one should be aware of it and know different ways to prevent it.
We hope this article has enlightened you about trap phishing, its types, and ways to prevent it. Feel free to share your queries in the comments section below.
People are also reading:




Leave a Comment on this Post